Routing any traffic via proxies improves the privacy factor even though it doesn’t assure security. It works by intercepting between the sending and receiving parties. This means the incoming data enters via a port and gets forwarded to the other network through another port. For those wanting to browse the internet with improved privacy and complete freedom finds solace in residential socks5 proxy. What exactly is it and why should you use it? Let’s find out.
What are SOCKS5 and SOCKS Proxies?
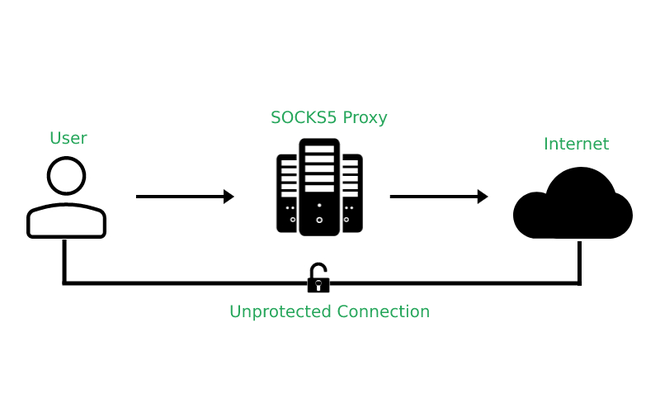
A SOCKS proxy or Socket Secure refers to an internet protocol that works by exchanging network packets between the server and the user through a proxy. Basically, it’s a means to veil the source of internet traffic. SOCKS has been designed for routing all forms of traffic generated by any program or protocol.
A SOCKS proxy generates a TCP or Transmission Control Protocol connection to a different server present behind the firewall on behalf of the user. Next, it exchanges the available network packets between the user and the original server. This facility is used since users remain behind the firewall and do not have permission to establish TCP connections to outward servers unless it is accessed through the SOCKS proxy server. This implies that a SOCKS proxy circulates a user’s TCP and UDP session with a firewall.
SOCKS forms a 5 layer protocol without caring about anything underneath the layer in the OSI model. This means the user won’t be able to use the same for tunneling protocols working under the 5 layer. From the perspective of security, it will prevent the attacker to perform scans through tools like Nmap when they try to scan through half-open connections as it works at the 5 layer.
Why should you invest in the SOCKS5 proxy?

1. Accessing Back-End Services behind the Firewall
Generally, the cloud hosts a cluster behind the firewall for bringing down potential security vulnerabilities. Two ways are available to access any backend services that run within a cluster although each comes with its own restrictions. It exposes backend services to the public and this releases it to the associated security risks. Next, it whitelists the user’s IP and allows traffic to backend services.
On the flip side, a residential SOCKS5 proxy with dynamic port forwarding with SSH can be a viable alternative to the undesired conditions mentioned above. The developer or administrator would be able to access the backend services within a cluster.
2. Doesn’t require any special setup
The most critical benefit of residential socks5 proxy is that it doesn’t require any special setup when you have access to SSH to the gateway of a cluster or the Edge node. As a result, developers and administrators will be able to access back-end resources behind the firewall through an SSH tunnel without a VPN.
3. Doesn’t require third-party free or public proxy server
As the residential SOCKS5 proxy helps to route all sorts of UPD and TCP traffic to the respective services via SSH tunneling, there is no need for 7-layer application-oriented special proxies for every service for routing the application process.
Compared to the various other application proxies, SOCKS5 needs not to rewrite those data packets. It only depends on the traffic between the various devices. As a result, it is not prone to flaws while boosting performances automatically.
Where to buy SOCKS5 and SOCKS proxies?
When it comes to choosing SOCKS5 proxies, it’s better to opt for trusted providers. You have to make sure that there is a wide array of proxies to select from. Once you establish your case, they must be able to deliver the perfect SOCKS5 proxy service.
Another important feature to look for is 24×7 tech support so that you will have professional assistance anytime you want. When you select a diligent SOCKS5 proxy, the manager will be able to address any concerns that you are facing.
Final words
With our lives becoming entirely spent online, ensuring digital security is extremely crucial. As long as you are on the internet, you are susceptible to vulnerability. This is true unless you are using highly secured network access through encrypted procedures like SOCKS5. It’s true data security and online encryption are available with most websites as a part of shielding themselves from hackers. But you cannot depend on them entirely and consider investing in SOCKS5 proxies.






